#517 Support for Verizon Jetpack MiFi 7730L?
new-hardware
Good morning,
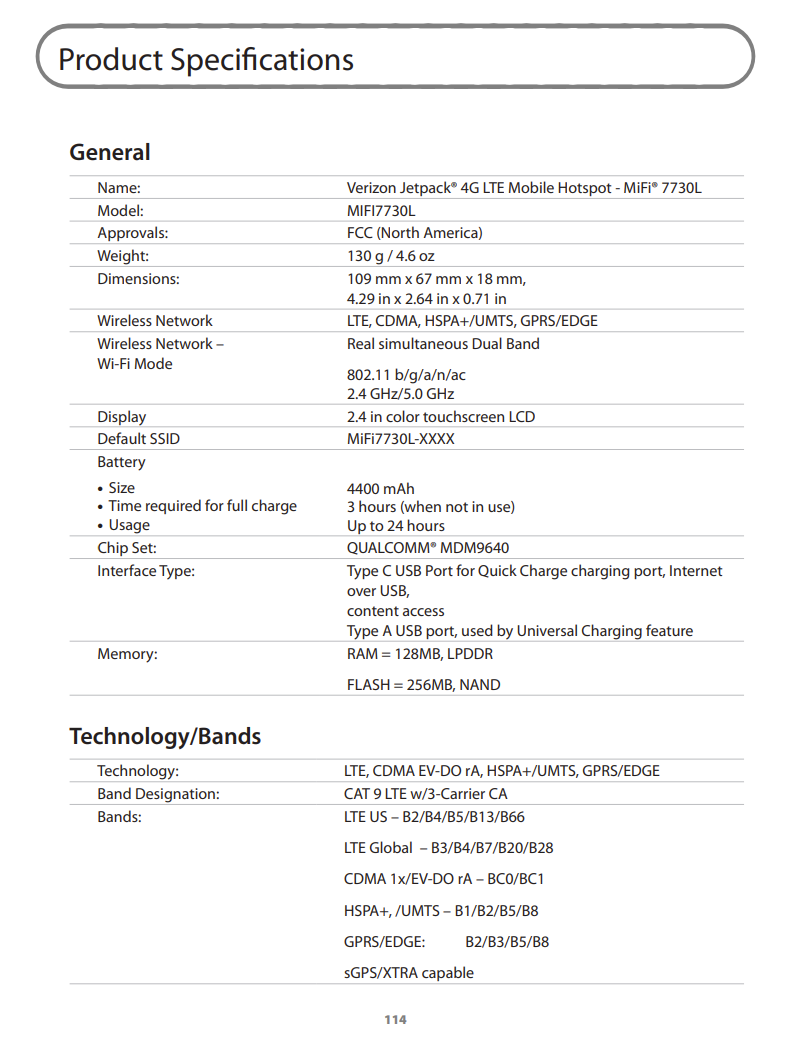
Thanks for building this – very cool. Is it possible to get support for the Verizon Jetpack MiFi 7730L? It seems that it runs a Qualcomm MDM9640. I have one on hand I could test or get information from if you can point me in the right direction (not sure how/what information is necessary.)
Thank you!
Device details:
https://ss7.vzw.com/is/content/VerizonWireless/Devices/Mifi/userguide/verizon-jetpack-mifi-7730l-ug.pdf
2
I found some info here: https://github.com/EFForg/rayhunter/discussions/484 and some commentary that’s insightful.
I’ll close this and re-open if I find anything useful / want to support it.
If the install process can be easily automated and rayhunter can get useful information & there’s enough storage space, we’d likely be quite happy to support the device. I have a 5530L and a 6620L that I haven’t taken a look at yet that probably have a very similar unlocking method & userspace.
I think it can be kept open if you want. it’s hard to tell whether this will work, usually we just poke around and see if there is a way to get adb shell on it somehow. places where to buy these devices cheap would be useful
Looks like they’re fairly inexpensive nowadays; I bought one years ago for a trip and it’s been kicking around on my desk: https://www.ebay.com/sch/i.html?_nkw=jetpack+7730L&_sacat=0&_from=R40&_sop=15 $15 or so
It does support tethering. Is there a good writeup for some step-by-step for how I could check if it’s possible to get an ADB shell? I can test/check via Linux or Windows.
not really, no two devices work the same. things that have worked in the past are:
<devicename> + telnet– particularly4pda.tois full of information for how to root various devices (though if this device only works in the US you might be out of luck there)adb shellwhile it’s plugged in and seeing what comes up$(busybox telnetd -l /bin/sh)it’s a creative process. you might want to read the existing code for the installer in rayhunter for inspiration.
adb shell achieved – I see what you mean about poking around.
.\mifilink.exe diagNote that I tried several different numeric options.\mifilink.exe 0/1/2/3/4/5/6and I didn’t get any that resulted in ADB access. I had to pull the battery to reset the device quite a few times.Ports (COM & LPT)and you’ll see a new COM port.nohup sh -c "export LD_LIBRARY_PATH=/opt/nvtl/lib; /opt/nvtl/bin/usb_cli stop && /opt/nvtl/bin/usb_cli start FTM" &and then the device will reboot. Note that I tried “LTM” like the 4pda.to link suggested and that didn’t work.adb shelland you’re inNotes: The root password seems to be unknown; once I had adb shell I just ran
suthenpasswdto change the root password to something else.Some references:
Edit: Based on the contents of
/opt/nvtl/bin/mifi_rootpass.shthe root password may bedijD31but since I reset mine, I cannot know for sure.i’m impressed by this turnaround time but also, that list of steps just to get rootshell is long. I feel that it’s not viable to maintain a cross-platform installer for it without trying to find a shortcut. some concerns:
mifilink.exeprobably has to be reverse-engineered with ghidra. we can’t bundle it in the installer even if we can somehow figure out how to run it on linux.Yea I agree – very manual. In lieu of main support, is there a way to test a bit further / try installing rayhunter on the device as a proof of concept?
I saw some chatter of “InseegoTool-0.7-jar-with-dependencies.jar” being able to do what mifilink.exe does, so I pulled a copy of that and looked. (https://www.decompiler.com/jar/c93a4f4589e54e9bb33f7823d9d09961/InseegoTool-0.7-jar-with-dependencies.jar) FWIW I did look at mifilink.exe as well but I don’t really understand it: https://dogbolt.org/?id=1bca6af9-fabb-47b4-a1f8-c11313cb71a7
When the device initially shows up with
mifilinkit reports as:Found 1410/b010 MiFi 8x00 (HID)After modification it shows up as:
Found 1410/b021 MiFi 7730 (HID)This tracks with the java code from what I can tell; it’s sending some command to the HID device with this hid4java library: https://github.com/gary-rowe/hid4java
I think the
DEBUG_MODEall 0’s array is why the 8x00 gets dropped.assuming the proof of concept succeeds and we see meaningful data in the pcap. it seems to me the main issue is how to make the installer simpler and easier to maintain.
maybe there is a shell injection vulnerability in the admin UI, similar to tplink? This would solve all problems. Now that you have root access you can find the binaries for the web interface and load them into ghidra.
I also just ordered a device for myself to play around with it
In case you wanted to take a look with ghidra ahead of time, I pulled the
/opt/nvtl/webuifolder. It seems like most things are flowing throughwebui.cgiper all of the redirects in/opt/nvtl/etc/webui/config.xml. webui.ziphey i grabbed the mifilink.exe file and my microsoft defender freaked out, is the site compromised or is it just a false flag?
What’s the signature that it detected, @TheHonoredDrunkShoko? Chinese manufacturer utilities often get picked up as malware like Wacatac because they’re written in stuff like .NET and use an obfuscator (to avoid theft of trade secrets, I presume) - you guessed it, in this example the obfuscator is the same one used by Wacatac.
looks like you were right, it marked “Wacatac.H!ml” as a trojan, glad to know im in the clear to continue. im brand new to this so im not really sure what to look out for and what to ignore, i really appreciate you replying and teaching me!
Proof of concept works I think?/The web interface at least loads. I probably didn’t do this the right way, but it does seem to be running. I manually executed the commands on the left to copy the files over and configure the services. For some reason they didn’t automatically start after the reboot. I was able to run them however and it loads up the interface!
Install / manually started services: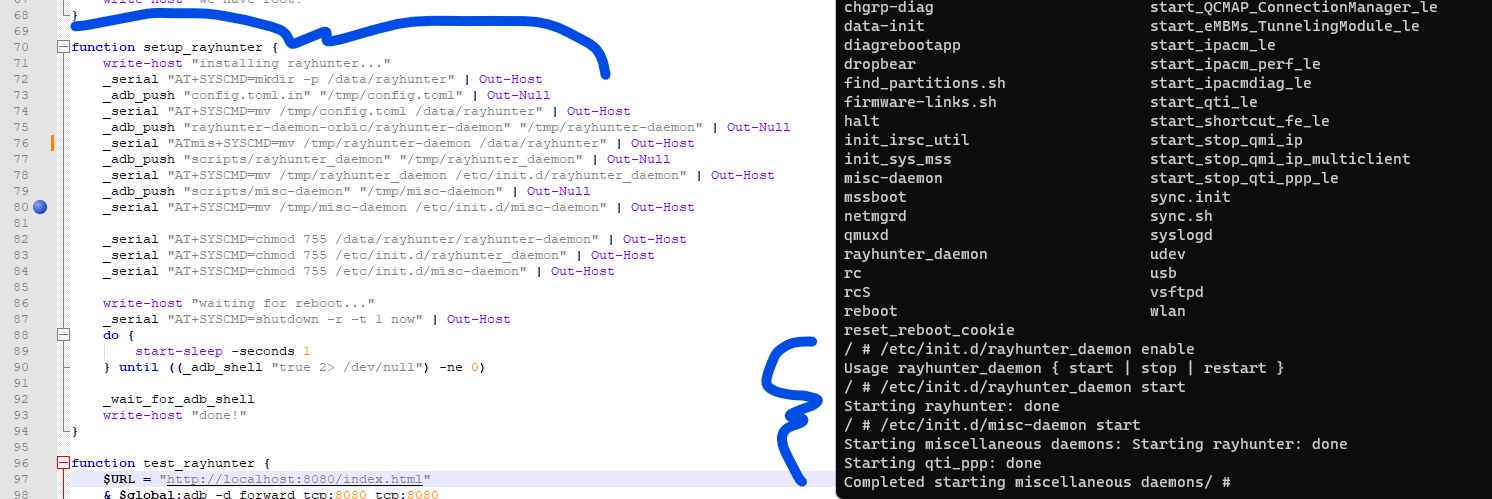
Loads! (Sort of interestingly I’m not sure how to get the time set because it doesn’t have an active SIM (hah!) so no upstream network connection.)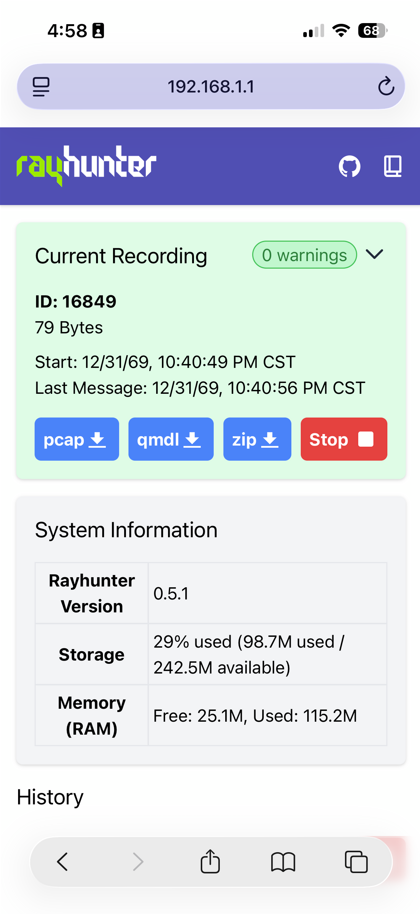
Attaching the pcap and qmdl files, but not sure there’s anything useful in there. Not sure how to actually test if it works. 16849.zip
that pcap seems to be empty, maybe let it run for longer and with a different SIM? maybe even an active one.
Active SIM returned some data! Not sure why the inactive SIM didn’t return any data. Active SIM:
Inactive SIM (after the active SIM was used):
You can see in
rayhunter.logthe cutover when the new SIM came up:I can’t seem to figure out how to run AT commands or why the daemons don’t start on boot. It captures data with an active SIM, and some data with an inactive SIM after the active one was used. I wonder if the issue was partially datetime related when the system didn’t have updated time information.
I have an Orbic with a Verizon SIM card that isn’t valid, i.e. it is denied attachment to Verizon’s network with EPS cause 8 (EPS services and non-EPS services not allowed.) It came with the Orbic when I purchased it from eBay. As per the “rules” of the modem, it only attempts to authenticate/attach to the tower once and then never again after getting that message, until it is rebooted.
Despite this, it is able to get the current time from the towers (probably through SIB8, field lte-rrc.systemTimeInfo - on average, one SIB8 message is sent every few minutes, so you wouldn’t get it immediately.) Therefore I doubt it’s an issue with the system clock being unset.
If you’re still curious, try:
To see output, run another adb shell in another terminal window and run
cat /dev/smd11in there.Interesting; seems to be some kind of issue with rootshell. But the AT commands work!
since you apparently can su from adb shell (according to an earlier comment of yours) I don’t think you need the rootshell. that’s a binary that’s pretty much specific to orbic imo
This is the point where I admit I first thought this was about the Orbic, then I retroactively edited my comments to ensure Orbic-specific stuff is labelled optional, and crossed my fingers hoping it works on other similar devices… 😂😂😂
But, yes, this is the way I was doing AT commands on the Orbic, so it will work there too.
‘’ The Jetpack Administrator has turned off access to the factory Reset feature. the physical reset button is also turned off. ‘’
I need help. I can’t enter my modem password in the interface, and I can’t even reset it. I’ve tried everything, nothing works.
‘’ The Jetpack Administrator has turned off access to the factory Reset feature. the physical reset button is also turned off. ‘’
I need help. I can’t enter my modem password in the interface, and I can’t even reset it. I’ve tried everything, nothing works.
Any update on this? I have a Mifi6620L that I’d like to use with Rayhunter.
that’s a different model i think. we don’t have plans to support new devices generally, it happens when there’s a large demand for it. instead of asking if there’s updates please just upvote the post.
Any luck with this? I have a 7730 and would love to give it new life.